[CompTIA] PT0-003 - Pentest+ Exam Dumps & Study Guide
# Complete Study Guide for the CompTIA PenTest+ (PT0-003) Exam
CompTIA PenTest+ (PT0-003) is the latest version of the intermediate-level certification designed to validate the knowledge and skills of IT professionals in conducting authorized penetration tests and security assessments across diverse environments. Whether you are a security analyst, a penetration tester, or a technical lead, this certification proves your ability to identify and exploit security vulnerabilities.
## Why Pursue the CompTIA PenTest+ Certification?
In an era of increasing cyber threats, organizations need highly skilled professionals to identify and protect their data and systems. Earning the PenTest+ badge demonstrates that you:
- Can conduct authorized penetration tests and security assessments across diverse environments.
- Understand the technical aspects of penetration testing and how to apply them to identify potential threats.
- Can analyze security risks and develop mitigation strategies for penetration tests.
- Understand the legal and regulatory requirements for data security and privacy in penetration testing.
- Can provide technical guidance on penetration testing-related projects.
## Exam Overview
The CompTIA PenTest+ (PT0-003) exam consists of multiple-choice and performance-based questions. You are given 165 minutes to complete the exam, and the passing score is typically 750 out of 900.
### Key Domains Covered:
1. **Planning and Scoping (14%):** This domain focuses on your ability to plan and scope authorized penetration tests. You'll need to understand different penetration testing models and how to design for high availability and reliability.
2. **Information Gathering and Vulnerability Identification (22%):** Here, the focus is on the technical implementation and management of information gathering and vulnerability identification. You must understand reconnaissance, scanning, and identification.
3. **Attacks and Exploits (30%):** This section covers your knowledge of attack techniques and exploit tools. You'll need to know how to install and configure various exploit tools.
4. **Reporting and Communication (18%):** This domain tests your ability to report and communicate penetration testing findings to various stakeholders. You must understand different types of documentation and how to follow them.
5. **Tools and Analysis (16%):** This domain focuses on your ability to use various tools and analysis techniques for penetration tests. You must be proficient with various penetration testing tools and techniques.
## Top Resources for PenTest+ Preparation
Successfully passing the PenTest+ requires a mix of theoretical knowledge and hands-on experience. Here are some of the best resources:
- **Official CompTIA Training:** CompTIA offers specialized digital and classroom training specifically for the PenTest+ certification.
- **PenTest+ Study Guide:** The official study guide provides a comprehensive overview of all the exam domains.
- **Hands-on Practice:** There is no substitute for conducting penetration tests. Set up your own home lab and experiment with different penetration testing architectures and tools.
- **Practice Exams:** High-quality practice questions are essential for understanding the intermediate-level exam format. Many candidates recommend using resources like [notjustexam.com](https://notjustexam.com) for their realistic and challenging exam simulations.
## Critical Topics to Master
To excel in the PenTest+, you should focus your studies on these high-impact areas:
- **Penetration Testing Infrastructure and Management:** Master the nuances of designing and conducting secure penetration tests across diverse environments.
- **Information Gathering and Vulnerability Identification:** Understand different information gathering and vulnerability identification techniques and tools.
- **Attacks and Exploits Techniques:** Master the principles of attack techniques and exploit tools and how to use them for penetration tests.
- **Reporting and Communication:** Know how to report and communicate penetration testing findings to various stakeholders.
- **Penetration Testing Security and Compliance:** Understand the security and compliance requirements for penetration testing and privacy.
## Exam Day Strategy
1. **Pace Yourself:** With 165 minutes for the exam, you have ample time. If a question is too complex, flag it and move on.
2. **Read the Scenarios Carefully:** Intermediate-level questions are often scenario-based. Pay attention to keywords like "most likely," "least likely," and "best way."
3. **Use the Process of Elimination:** If you aren't sure of the right choice, eliminating the wrong ones significantly increases your chances.
## Conclusion
The CompTIA PenTest+ (PT0-003) is a significant investment in your career. It requires dedication and a deep understanding of penetration testing principles and technical skills. By following a structured study plan, leveraging high-quality practice exams from [notjustexam.com](https://notjustexam.com), and gaining hands-on experience, you can master the complexities of penetration testing and join the elite group of certified penetration testers.
Free [CompTIA] PT0-003 - Pentest+ Practice Questions Preview
-
Question 1
A penetration tester wants to send a specific network packet with custom flags and sequence numbers to a vulnerable target. Which of the following should the tester use?
- A. tcprelay
- B. Bluecrack
- C. Scapy
- D. tcpdump
Correct Answer:
C
Explanation:
I agree with the community choice of C. Scapy is the industry-standard tool for packet manipulation and crafting, offering granular control over every field in the network stack, which is exactly what the scenario requires.
Reason
Scapy is a Python-based tool that enables users to forge or decode packets of a wide number of protocols, send them on the wire, capture them, and match requests and replies. It is specifically designed to handle tasks that classic tools cannot, such as sending packets with invalid sequence numbers or custom TCP flags for advanced scanning and exploitation.
Why the other options are not as suitable
- Option A is incorrect because tcprelay is typically used to relay or redirect TCP connections from one host to another rather than crafting individual custom packets from scratch.
- Option B is incorrect because Bluecrack is a tool specifically used for Bluetooth PIN cracking and does not serve as a general-purpose network packet crafter.
- Option D is incorrect because tcpdump is a packet analyzer and sniffer used to capture and display network traffic; it lacks the native capability to craft and transmit custom packets with specific flags.
Citations
-
Question 2
Which of the following explains the reason a tester would opt to use DREAD over PTES during the planning phase of a penetration test?
- A. The tester is conducting a web application test.
- B. The tester is assessing a mobile application.
- C. The tester is evaluating a thick client application.
- D. The tester is creating a threat model.
Correct Answer:
D
Explanation:
I agree with the community choice of Option D. DREAD is a specific qualitative risk assessment model used to score and prioritize threats during the threat modeling process, whereas PTES is a comprehensive methodology covering the entire execution lifecycle of a penetration test.
Reason
Option D is correct because DREAD (Damage, Reproducibility, Exploitability, Affected users, Discoverability) is a framework explicitly designed for threat modeling. During the planning phase, if a tester needs to quantify the risk of specific threats to determine which ones to prioritize for exploitation, DREAD provides the granular scoring system required for that task.
Why the other options are not as suitable
- Option A is incorrect because the type of test (web application) does not dictate the use of DREAD; while DREAD can be used for web apps, it is a risk-scoring tool, not a web-specific methodology like OWASP.
- Option B is incorrect because mobile application assessments typically follow methodologies like OWASP MASTG, and selecting DREAD is based on the need for risk prioritization rather than the platform being tested.
- Option C is incorrect because thick client testing, like other targets, refers to the scope of the engagement; the choice of DREAD is driven by the specific activity of threat modeling and risk ranking, not the software architecture.
Citations
-
Question 3
A penetration tester is performing a security review of a web application. Which of the following should the tester leverage to identify the presence of vulnerable open-source libraries?
- A. VM
- B. IAST
- C. DAST
- D. SCA
Correct Answer:
D
Explanation:
I agree with the suggested answer D (SCA). Software Composition Analysis is the industry-standard methodology for identifying third-party dependencies and comparing them against known vulnerability databases (such as CVEs).
Reason
SCA (Software Composition Analysis) is specifically designed to scan an application's source code, package manifests, or binaries to create a Bill of Materials (BOM). It identifies open-source libraries, their versions, and checks if those versions contain documented security vulnerabilities or licensing issues.
Why the other options are not as suitable
- Option A is incorrect because VM (Vulnerability Management) is a broad process or lifecycle for identifying, prioritizing, and remediating vulnerabilities across an entire enterprise infrastructure, not a specific tool for library analysis.
- Option B is incorrect because IAST (Interactive Application Security Testing) uses agents within the application at runtime to identify vulnerabilities in the functional code logic; while it has some visibility, it is not the primary tool for dependency inventory.
- Option C is incorrect because DAST (Dynamic Application Security Testing) interacts with the application from the outside in a running state (black-box) to find exploitable flaws like SQLi or XSS, but it cannot see the internal library versions or source code components directly.
Citations
-
Question 4
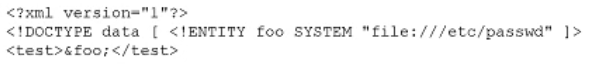
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
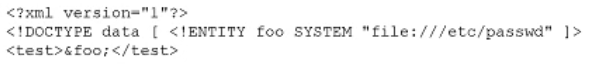
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
- A. Drop all excessive file permissions with chmod o-rwx.
- B. Ensure the requests application access logs are reviewed frequently.
- C. Disable the use of external entities.
- D. Implement a WAF to filter all incoming requests.
Correct Answer:
C
Explanation:
I agree with the suggested answer C. The payload shown is a classic XML External Entity (XXE) injection attack, which leverages a misconfigured XML parser to read local system files. Disabling the resolution of external entities is the industry-standard remediation for this vulnerability.
Reason
Option C is correct because the root cause of an XXE vulnerability is the XML parser's willingness to process Document Type Definitions (DTDs) that contain external entity references. By configuring the parser to disable external entities (specifically the SYSTEM identifier), the application will ignore requests to fetch local or remote resources, effectively neutralizing the threat at the source.
Why the other options are not as suitable
- Option A is incorrect because while restricting file permissions is a defense-in-depth measure, it does not fix the underlying software vulnerability; the application still requires read access to many files to function, which could still be leaked.
- Option B is incorrect because log review is a detective control, not a preventative control; it identifies that an attack occurred but does not stop the data from being exfiltrated.
- Option D is incorrect because a WAF is a perimeter control that can often be bypassed with encoding or alternative XML structures; the most robust 'best' recommendation is to fix the application code itself.
Citations
-
Question 5
A penetration tester is conducting reconnaissance for an upcoming assessment of a large corporate client. The client authorized spear phishing in the rules of engagement. Which of the following should the tester do first when developing the phishing campaign?
- A. Shoulder surfing
- B. Recon-ng
- C. Social media
- D. Password dumps
Correct Answer:
C
Explanation:
I agree with the community and suggested answer of Option C. Spear phishing requires highly specific, personalized intelligence about targets to be successful, and social media platforms are the premier source for harvesting these details.
Reason
Option C is correct because spear phishing is a targeted attack. To execute it, a tester must identify specific individuals, their job titles, professional relationships, and interests. Platforms like LinkedIn and Facebook provide the necessary Open-Source Intelligence (OSINT) to build a convincing narrative and target list for a corporate environment.
Why the other options are not as suitable
- Option A is incorrect because shoulder surfing is a physical social engineering technique used to observe a victim's screen or keyboard in person; it is not a primary or efficient method for gathering the wide-scale reconnaissance needed for a phishing campaign.
- Option B is incorrect because while Recon-ng is a powerful reconnaissance framework, it is a tool used to automate the collection of data (often from social media APIs), but it is not the data source itself; the fundamental activity is the gathering of social media information.
- Option D is incorrect because password dumps are useful for credential stuffing or understanding password complexity, but they do not provide the contextual personal information required to develop a tailored spear phishing lure.
Citations
-
Question 6
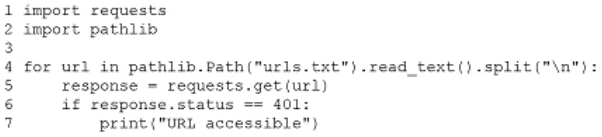
A penetration tester needs to test a very large number of URLs for public access. Given the following code snippet:
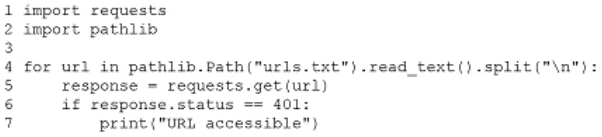
Which of the following changes is required?
- A. The condition on line 6
- B. The method on line 5
- C. The import on line 1
- D. The delimiter in line 3
Correct Answer:
A
Explanation:
I agree with the suggested answer A. The code snippet contains two significant issues on line 6: a logical error where it equates 'accessible' with a 401 Unauthorized status, and a syntax error because the requests library uses the attribute status_code, not status.
Reason
Option A is correct because line 6 is fundamentally flawed for the intended task. First, the requests library returns an object where the HTTP status is stored in the status_code property; .status would raise an AttributeError. Second, a 401 status indicates the resource is protected/unauthorized, which contradicts the print statement 'URL accessible'. To test for public access, the condition should typically check for a 200 OK status or use response.ok.
Why the other options are not as suitable
- Option B is incorrect because the requests.get(url) method on line 5 is a standard and valid way to retrieve a URL in Python. While a head() request might be faster for large volumes, get() is functionally correct for testing connectivity.
- Option C is incorrect because import requests is the correct syntax for importing the necessary library to perform HTTP requests.
- Option D is incorrect because .split("
Citations
-
Question 7
During a penetration test, a tester captures information about an SPN account. Which of the following attacks requires this information as a prerequisite to proceed?
- A. Golden Ticket
- B. Kerberoasting
- C. DCShadow
- D. LSASS dumping
Correct Answer:
B
Explanation:
I agree with the community choice of Option B. A Service Principal Name (SPN) is the unique identifier that Kerberos uses to associate a service instance with a service account in Active Directory. Identifying accounts with SPNs is the foundational step of a Kerberoasting attack.
Reason
Kerberoasting is a post-exploitation technique where an attacker requests a service ticket (TGS) for any account with a registered SPN. Because the ticket is encrypted with the service account's password hash, the attacker can extract the hash from the ticket and attempt to crack it offline. Capturing SPN information is the prerequisite to identifying which accounts can be targeted for this request.
Why the other options are not as suitable
- Option A is incorrect because a Golden Ticket attack involves forging a Ticket Granting Ticket (TGT), which requires the NTLM hash of the KRBTGT account, not SPN information.
- Option C is incorrect because DCShadow involves simulating a Domain Controller to push malicious changes to Active Directory via replication; while it requires high-level privileges, it is not predicated on capturing SPN data.
- Option D is incorrect because LSASS dumping is a local credential harvesting technique used to extract cleartext passwords or hashes from memory (Local Security Authority Subsystem Service) and does not rely on SPN lookups.
Citations
-
Question 8
While performing an internal assessment, a tester uses the following command: crackmapexec smb 192.168.1.0/24 -u user.txt -p Summer123@
Which of the following is the main purpose of the command?
- A. To perform a pass-the-hash attack over multiple endpoints within the internal network
- B. To perform common protocol scanning within the internal network
- C. To perform password spraying on internal systems
- D. To execute a command in multiple endpoints at the same time
Correct Answer:
C
Explanation:
I agree with the community consensus that Option C is the correct answer. The command structure identifies a classic password spraying pattern by pairing a large list of usernames (user.txt) with a single, static password (Summer123@) across an entire subnet.
Reason
Option C is correct because password spraying is defined by attempting a single password against many different accounts to bypass account lockout thresholds. In the provided CrackMapExec (CME) command, the -u flag points to a file containing multiple usernames while the -p flag provides one specific password, perfectly matching this attack methodology.
Why the other options are not as suitable
- Option A is incorrect because a pass-the-hash attack requires the --hash flag and an NTLM hash string; this command uses a plaintext password.
- Option B is incorrect because while CrackMapExec does perform scanning and enumeration, the inclusion of credentials (-u and -p) indicates that the primary purpose is an active authentication attack rather than general service discovery.
- Option D is incorrect because executing commands on endpoints requires specific flags like -x or --exec-method, which are absent from this syntax; this command only tests authentication success.
Citations
-
Question 9
A penetration testing team needs to determine whether it is possible to disrupt the wireless communications for PCs deployed in the client's offices. Which of the following techniques should the penetration tester leverage?
- A. Port mirroring
- B. Sidecar scanning
- C. ARP poisoning
- D. Channel scanning
Correct Answer:
D
Explanation:
I agree with the community and suggested answer of D. Channel scanning. To disrupt wireless communications, a tester must first identify the RF environment, including active frequencies and 802.11 channels. Channel scanning is the foundational step for assessing the feasibility of attacks like jamming or deauthentication.
Reason
Channel scanning is the correct technique because it allows the penetration tester to discover the specific radio frequencies and SSIDs in use by the client. By identifying which channels are active (e.g., in the 2.4GHz or 5GHz bands), the tester can determine where to focus interference or deauthentication efforts to effectively disrupt connectivity.
Why the other options are not as suitable
- Option A is incorrect because port mirroring (or SPAN) is a wired networking technique used on switches to copy traffic from one port to another for analysis; it does not impact or assess wireless RF availability.
- Option B is incorrect because sidecar scanning generally refers to architectural patterns in containerized environments or specific side-channel analysis, neither of which is a standard method for testing wireless communication disruption.
- Option C is incorrect because ARP poisoning is a Layer 2 Man-in-the-Middle (MitM) attack used to redirect traffic on a local network; while it can occur over a wireless connection once associated, it does not disrupt the wireless communication medium itself.
Citations
-
Question 10
Which of the following tasks would ensure the key outputs from a penetration test are not lost as part of the cleanup and restoration activities?
- A. Preserving artifacts
- B. Reverting configuration changes
- C. Keeping chain of custody
- D. Exporting credential data
Correct Answer:
A
Explanation:
I agree with the community consensus that Option A is the correct answer. In the context of CompTIA PenTest+ (PT0-003), the post-engagement phase requires a careful balance between cleaning up the environment and ensuring all evidence needed for the final report is secured.
Reason
Preserving artifacts refers to the collection and safeguarding of evidence such as screenshots, terminal logs, exploit output, and reproduction steps. Since cleanup activities involve deleting temporary files and restoring system states, the tester must first ensure these 'key outputs' are moved to a secure, persistent location to justify findings in the final report.
Why the other options are not as suitable
- Option B is incorrect because reverting configuration changes is a primary goal of the cleanup phase itself, which involves removing the 'footprints' of the test, but it does nothing to save the data needed for the report.
- Option C is incorrect because chain of custody is a forensic procedure used to track evidence for legal proceedings; while important in some contexts, it is not the specific task used to prevent the loss of general pentest outputs during restoration.
- Option D is incorrect because exporting credential data is often restricted by the Rules of Engagement (RoE) and data handling requirements; while credentials may be proof of access, 'artifacts' is the broader and more appropriate term for all test outputs.
Citations